Nyroxis Endpoint SIEM
• Correlation-driven detection and real-time alerting
• Behavioral indicators for anomalous and malicious activity
• Encrypted event storage with integrity and tamper resistance
• Forensic-ready evidence collection and retention
• Designed for minimal noise and operational clarity
• Optional AI Copilot via nyroxis.ai plain-language alert analysis for non-technical users
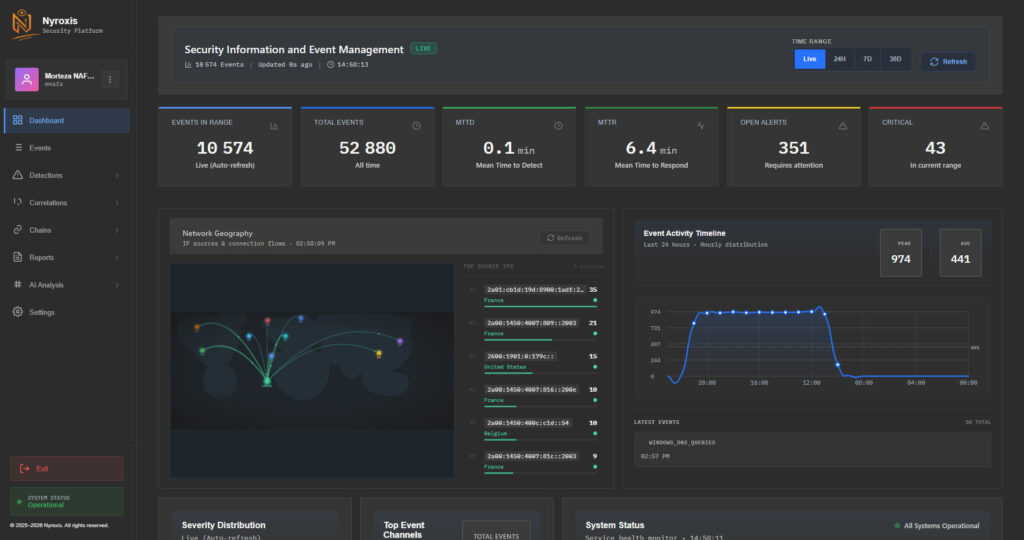
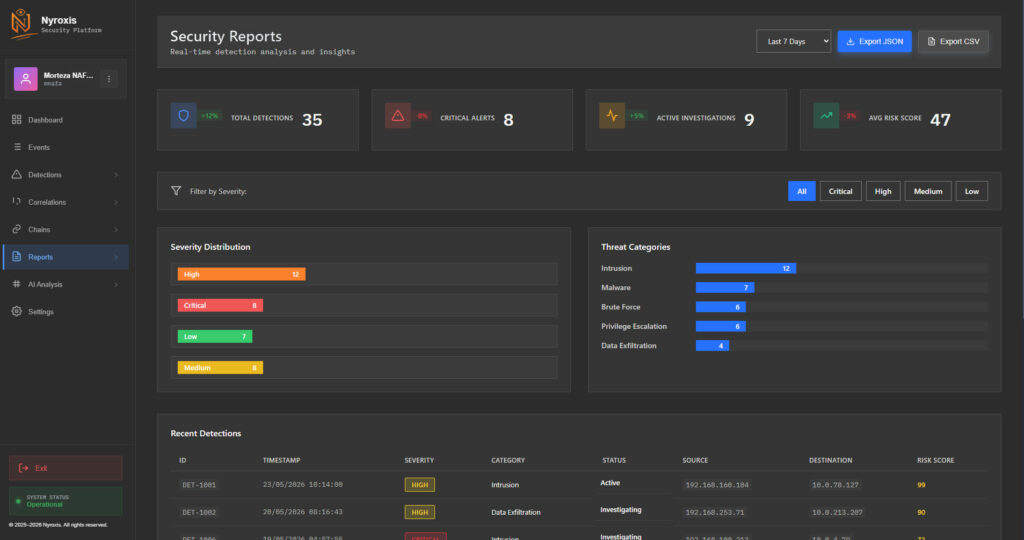
About Nyroxis SIEM
- Traditional antivirus solutions detect and remove known malicious files — and stop there. They react after the damage is done, with no forensic trail and no visibility into what an attacker actually did inside your system. Nyroxis takes a different approach. Built as a personal endpoint SIEM, it continuously collects, normalizes, and correlates system logs in real time across 27 detection rules, 12 correlation rules, and 2 chain rules — a library that grows continuously. Security professionals can also write and deploy their own custom rules, tailoring detection to their specific environment without modifying the core system. When a threat is detected, Nyroxis does not simply block it. It records and preserves the full attack sequence — delivering forensic-grade evidence, entirely offline, entirely on your device.
- ⚠️ About the GitHub Version — The Nyroxis repository on GitHub is a minimal Python proof-of-concept, created solely to establish a public timestamp for the Nyroxis name. It bears no resemblance to the actual platform. The GitHub version exists for reference only and should not be used to evaluate the real product.
Stay ahead of threats with Nyroxis
Live Threat Detection
Continuous surveillance of your processes, network, registry, and file system — detecting suspicious activity the moment it occurs. Fully offline — no cloud, no data transfer. Your data never leaves your device.
GDPR
Built from the ground up with GDPR compliance in mind. All data is encrypted locally, never transmitted, never shared. Your privacy is not a feature — it's the foundation.
AI-Powered Alert Analysis
Not sure what an alert means? Connect optionally to nyroxis.ai for plain-language explanations powered by Claude AI — no cybersecurity expertise required.
If you or a family member handle sensitive information and operate beyond the scope of ordinary individuals.

Your Next-Level Cyber Defense
Absolute Cyber Vigilance
Nyroxis is a local, silent SIEM system designed for complete monitoring of system activities. It logs and analyzes all suspicious events without interfering with system performance — ideal for high-risk environments and sensitive roles where accurate evidence collection is critical.
--- FIVE CORE MODULES ---
Network Activity Tracking
Process Monitoring
Critical File Integrity Checks
USB & Registry Activity Tracking
Suspicious Event Correlation Engine

Advanced Security Challenges
With customizable alert rules, Nyroxis allows you to instantly detect targeted threats. From monitoring dangerous keywords in PowerShell to spotting unusual USB activity, everything is logged and analyzed in real time.
--- FIVE INTELLIGENT FEATURES ---
Advanced log filtering and search
Multi-level alerts (Critical, Warning, Info)
Multilingual interface (FR/EN/DE)
CSV/JSON export for external analysis
Database optimization and maintenance

New Era, New Defense
Step into the new era of cybersecurity with Nyroxis. Operating silently, fully offline, and without any central server dependency, it ensures security in any environment. From hidden honeypots to legally admissible evidence collection — all in one lightweight, intelligent solution.
--- FIVE STERATEGIC ADVANTAGES ---
No alerting the attacker (Stealth Mode)
Timestamped, legally valid evidence collection
Fully offline operation
Compatibility with sensitive environments
Future integration with central SIEM

Professional Achievements
Incidents That Could Have Been Prevented with Nyroxis
LastPass Breach (2022)
In 2022, attackers compromised the personal home computer of a senior DevOps engineer at LastPass. By installing malware, they gained access to sensitive company vaults stored in the cloud. If Nyroxis had been installed on that home device: Suspicious PowerShell executions and unusual network activity could have been detected and alerted before the breach escalated.
Colonial Pipeline Ransomware Attack 2021
Hackers gained entry to Colonial Pipeline’s network by using login credentials stored on an employee’s personal device. This led to the shutdown of the largest fuel pipeline in the United States for several days. If Nyroxis had been on the employee’s home computer: Unusual VPN connections and abnormal login attempts would have been flagged instantly.
SolarWinds Supply Chain Attack 2020
In this major supply chain attack, intruders first breached personal systems used by some SolarWinds staff. They then inserted malicious code into an official software update, which was distributed to thousands of organizations. If Nyroxis had been installed on those personal systems: Unauthorized executable transfers and suspicious system modifications could have been detected early.
Target Data Breach 2013
Attackers infiltrated Target’s network through a third-party contractor’s personal computer, which was used to connect remotely to the company. This resulted in the theft of millions of customers’ credit card records. If Nyroxis had been on the contractor’s system: Unauthorized network connections and unusual traffic patterns would have triggered alerts before the intrusion succeeded.
Nyroxis Security Plans
Secure your personal and work devices with our advanced offline security monitoring system
Whether you’re an individual, a family member of a sensitive role, or part of a high-security environment, Nyroxis keeps you protected without alerting attackers.
FREE PLAN – Community Edition (Windows)
For personal use & open-source community testingGithub version
ENTERPRISE PLAN – Pro Edition (Multi-Platform)
Full feature set for professionals, VIPs, high-security environmentsContact Us
Threat Intelligence Feed
China-Linked JDY Botnet Expands to 1,500+ Devices for Cyber Reconnaissance
Cybersecurity researchers have warned of a “resurgence and expansion” of JDY, a covert network associated with China-nexus state-sponsored threat actors. “The JDY botnet comprises over… Read MoreThe Hacker News
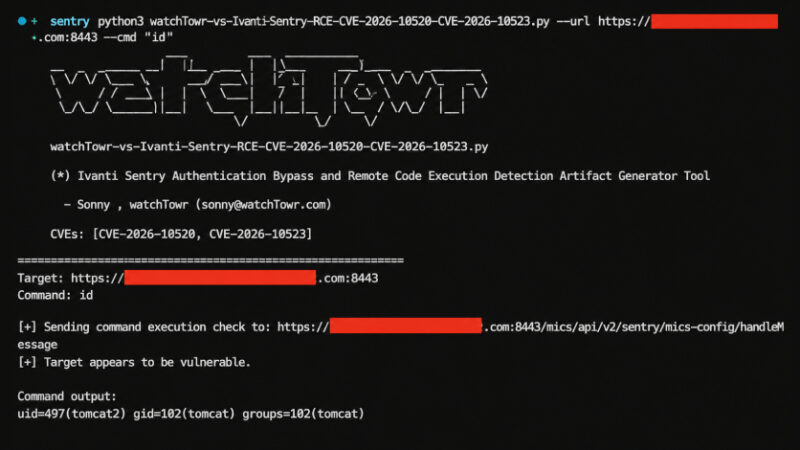
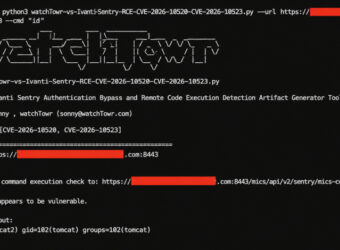
Ivanti, Fortinet, and SAP Release Patches for Multiple Critical Vulnerabilities
Fortinet, Ivanti, and SAP have released security updates to address multiple critical security vulnerabilities that could result in arbitrary code execution and information disclosure. The… Read MoreThe Hacker News

Unpatched Langflow Flaw CVE-2026-5027 Exploited for Unauthenticated RCE
A high-severity unpatched security flaw in Langflow, an open-source low-code platform to build artificial intelligence (AI) applications, has come under active exploitation in the wild,… Read MoreThe Hacker News

CISA Adds Cisco, Chrome, and Arista Flaws to KEV Catalog Amid Active Exploitation
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added three new vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, following reports of active… Read MoreThe Hacker News

Your Automated Pentest Looks Clean. See What It Missed in This Expert Webinar
Your pentest report looks clean. That might be the problem. Run automated pentesting long enough, and the new findings start to dry up. By the… Read MoreThe Hacker News

Meta to Use Off-Site Business Data for Feed and AI Personalization
Meta on Tuesday announced that it will use information shared by other businesses to personalize users’ feed and responses from its artificial intelligence (AI) chatbot,… Read MoreThe Hacker News